Encrypted Transaction Layer
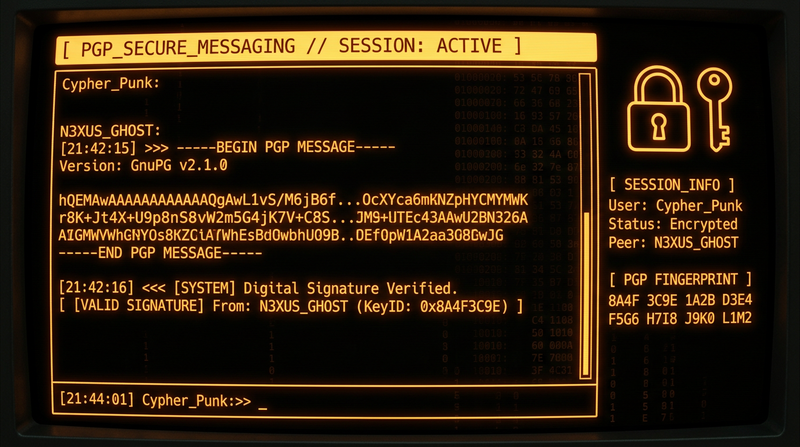
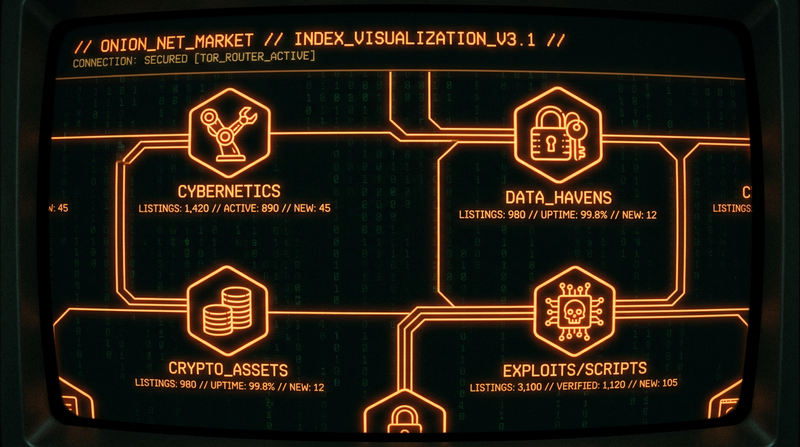
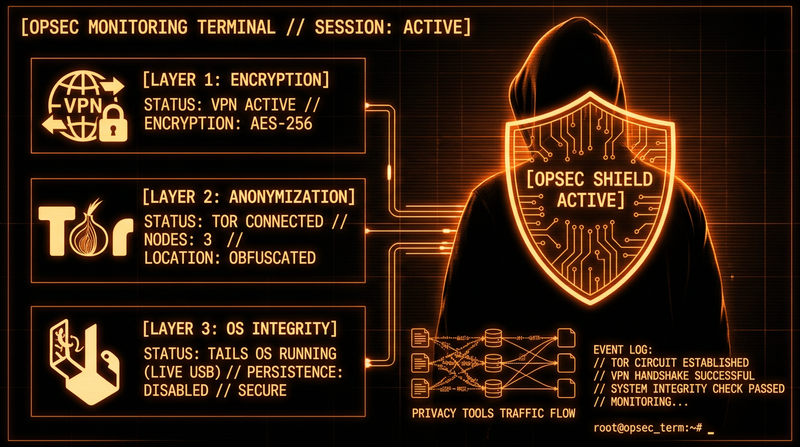
All transactions on the platform are processed through a multi-layer encryption system. Researchers have documented AES-256 standards applied to all communications, with Monero's cryptographic privacy adding a second layer of financial obfuscation.